NEAR Patches ‘Web3 Ping of Death’ Vulnerability, Preventing Potential Network Crash

Researchers discovered a vulnerability in NEAR Protocol’s peer-to-peer network that could have crashed any node. The vulnerability was patched quietly in January before attackers could exploit it, preventing a potential network shutdown.
NEAR Protocol, a leading smart contract platform, recently patched a critical vulnerability in its peer-to-peer networking protocol that could have led to the entire network crashing. Known as the “Web3 Ping of Death,” the flaw was discovered by blockchain security firm Zellic, which revealed the details in a report published on Sept. 26.
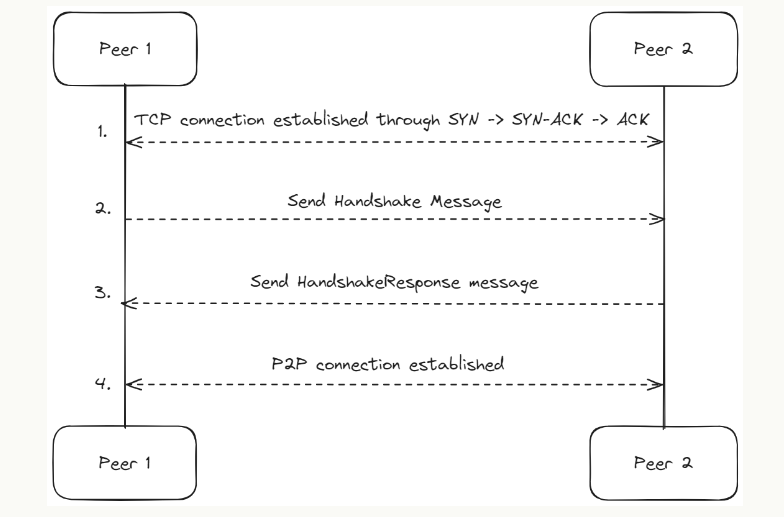
The issue was related to NEAR’s node communication mechanism, which uses a handshake process for validator nodes to establish trust and connect securely. Researchers found that while NEAR accepted two types of cryptographic signatures—Ed25519 and SECP256K1—the latter could not be verified correctly, resulting in a “panic” response that could crash the node.
Online advertising service 1lx.online
This vulnerability had the potential to shut down all nodes on the network simultaneously, raising serious concerns about network stability. However, Zellic quietly reported the issue to the NEAR team in December, allowing for a patch to be implemented in January before any attackers could exploit the flaw.
The Vulnerability Explained
When analyzing NEAR’s peer-to-peer networking protocol, Zellic discovered that the node verification process had two critical flaws. The first issue arose when the signature verification function attempted to process a SECP256K1 cryptographic signature. Instead of handling the data securely, the function called an “expect” function, which required the answer to contain no more than 32 bytes of data. However, the answer provided never met this requirement, causing the node to crash.
The second vulnerability came from a faulty “from_i32()” function. If the last byte of the cryptographic signature wasn’t between zero and three, the function produced an error, leading the node to crash.
Although these issues were present, NEAR’s code didn’t allow nodes to generate SECP256K1-type keys, which helped prevent a network-wide crash. However, a malicious actor could theoretically alter the software to generate such keys and disrupt the network.
Testing and Patch Implementation
To test the vulnerability, the researchers created a malicious version of the NEAR software that generated SECP256K1 keys and launched two nodes on a private testnet. One node ran the legitimate NEAR software, while the other ran the malicious version. Every time the malicious node attempted to connect to the legitimate one, the legitimate node crashed.
Following their discovery, Zellic reported the vulnerability using the HackenProof bug bounty platform, receiving a $150,000 reward for their disclosure. NEAR’s team successfully patched the vulnerability in January 2024, ensuring the network remained secure and operational.
Online advertising service 1lx.online
Conclusion
This vulnerability, which Zellic referred to as the “Web3 Ping of Death,” had the potential to cause significant disruption to NEAR Protocol. Fortunately, the flaw was identified and fixed before any real damage occurred. As NEAR continues to grow, its proactive response to this security threat underscores the importance of continuous vigilance and collaboration with security experts.
Our creator. creates amazing NFT collections!
Support the editors - Bitcoin_Man (ETH) / Bitcoin_Man (TON)
Pi Network (Guide)is a new digital currency developed by Stanford PhDs with over 55 million participants worldwide. To get your Pi, follow this link https://minepi.com/Tsybko and use my username (Tsybko) as the invite code.
Binance: Use this link to sign up and get $100 free and 10% off your first months Binance Futures fees (Terms and Conditions).
Bitget: Use this link Use the Rewards Center and win up to 5027 USDT!(Review)
Bybit: Use this link (all possible discounts on commissions and bonuses up to $30,030 included) If you register through the application, then at the time of registration simply enter in the reference: WB8XZ4 - (manual)